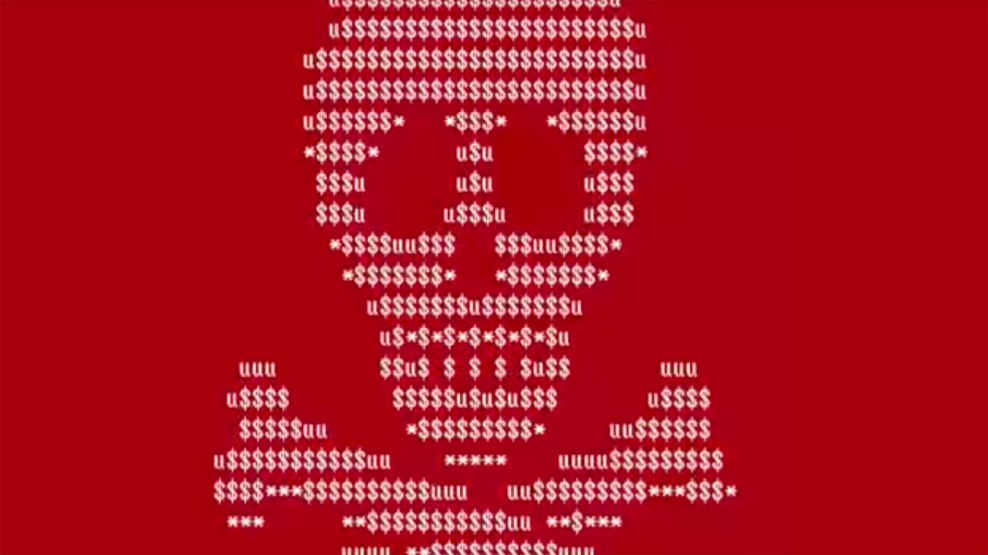
The Petya ransomware in actionDS-Tech/YouTube
A month after the WannaCry ransomware hobbled hundreds of thousands of computers around the world, another major ransomware attack is making its way across Europe, Russia, the United States, and elsewhere—locking the victims’ computers and demanding ransom payments.
“We are talking about a cyberattack,” Anders Rosendahl, a spokesman for A.P. Moller-Maersk, a massive Danish shipping company, told the Associated Press after the firm was hit by the malicious software. “It has affected all branches of our business, at home and abroad.”
According to cybersecurity firm Symantec, the attack makes use of the “EternalBlue” exploit developed by the National Security Agency called to take advantage of a flaw in the Microsoft Windows operating system. (Microsoft recently released a patch intended to address this flaw.) That exploit made its way into the wild after a group calling itself The Shadow Brokers dumped what it said was a suite of NSA hacking tools on the internet in April. The Shadow Brokers first came on the scene in August 2016 when they claimed to have hacked a server containing a host of tools used by the Equation Group, a hacking group thought to be associated with the NSA.
Initial reports dubbed the attack “Petya,” a version of previously detected malware, but information security firm Kaspersky Lab said Tuesday’s attack was something “that has not been seen before,” according to Patrick O’Neill of Cyberscoop.
Whoever was behind Tuesday’s wave of ransomware apparently demanded $300 worth of Bitcoin to unlock the affected computers. “If you see this text, then your files are no longer accessible because they have been encrypted,” the attackers wrote in a message posted on a victim’s computer screens. “Perhaps you are busy looking for a way to recover your files, but don’t waste your time. Nobody can recover your files without our decryption service.”
As of about 2 p.m. ET Tuesday, 24 payments had been made to the address listed by the hackers, totaling about $6,000.
Esto es lo que las víctimas del #ransomware #Petya han visualizado: pic.twitter.com/BpkRKXQPO9
— Enrique Serrano (@EnriqueITE) June 27, 2017
Merck, a US-based pharmaceutical company, said Tuesday that its computer network was also damaged “as part of the global hack” and that the company was investigating the matter. DLA Piper, a US-based global law firm, had its phones and computers affected by the bug. The Chernobyl nuclear power plant also reportedly switched to manual radiation monitoring because of the attack. Rosneft, a massive Russian energy company, said it had been impacted, as well.