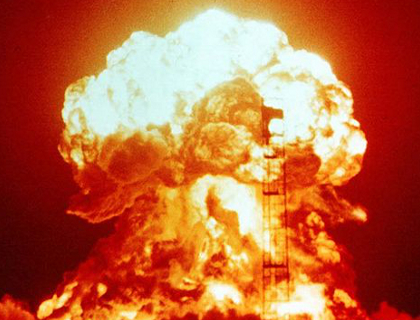
Wikimedia Commons
The Department of Energy, which is responsible for safeguarding America’s nuclear weapons and secrets, has failed to tell law enforcement the details of when its computer systems have come under attack, “hindering investigations” into some of the 2,300 cybersecurity incidents the agency recorded between October 2009 and March 2012. This lack of timely and comprehensive cybersecurity reporting is putting the DOE’s “information systems and networks at increased risk,” according to a new investigation by the agency’s internal watchdog.
The findings are “very problematic,” says James Lewis, a senior cybersecurity expert at the Center for Strategic and International Studies, because “DOE sites are a primary target for espionage and have been successfully hacked in the past.”
While preparing the report, the DOE’s Office of Inspector General audited seven sites, including nuclear laboratories at Los Alamos and the Savannah River Site in South Carolina, and found that, of 223 incidents reported at DOE sites, 41 percent were not reported within established time frames. Another 10 incidents involving a loss of personally identifiable information (which affected 109 people) were reported late.
Joshua McConaha, a spokesman for the National Nuclear Security Administration (NNSA), the DOE entity responsible for the nation’s nuclear weapons stockpile, told Mother Jones that the cybersecurity incidents not involving identity theft “were normal computer issues such as viruses” that occur “on a regular basis.” But experts say that the report’s findings still don’t bode well for nuclear weapons security.
Steven Aftergood, the director of the Project on Government Secrecy at the Federation of American Scientists, says that while the weapons themselves weren’t at risk, “weapons-related information and facility security information could potentially be vulnerable.” It wouldn’t be the first time: In 2007, hackers believed to be from China launched a sophisticated cyberattack on several DOE laboratories in the United States. A spokesman for Los Alamos National Lab, which undertakes nuclear weapons design, told ABC News that “a significant amount of data was removed” from a small number of computers on the facility’s unclassified network. This is the same lab that had its director step down in 2003 after a scandal involving widespread theft and security lapses.
Kevin Roark, a spokesman for Los Alamos National Laboratory, denies that the lab is reporting cyberattacks incorrectly. He told Mother Jones that the audit listed “six incidents where they believed Los Alamos was late in its reporting,” none of which had to do with personal information being stolen. And according to Roark, “Los Alamos personnel have subsequently checked the six incidents, and determined that all were reported within the required time frame, but the information in the reports led the reporting authority to derive an inaccurate date and time.”
When asked to about the incidents and Roark’s response, a spokesman for the IG said that “the report speaks for itself and we have no additional comment.”
It’s well established that the NNSA faces regular cyberattacks—a spokesman for the agency told US News and World Report in March that if you count “security significant cyber security events,” the number of cyberattacks goes up to 10 million per day. (Experts told Mother Jones that the number changes depending on how you categorize different types of incidents.) The real question is whether NNSA and DOE can deal with the attacks. The DOE has recently taken steps like improving cybersecurity training for employees and addressing weaknesses at facilities, according to a separate report released by the inspector general last month.
“Cybersecurity is a work in progress, both inside and outside government.” Aftergood notes. ” One would like to think that the nuclear weapons infrastructure would be ahead of the curve, but apparently that is too much to expect.”
Left unanswered is the question of who’s to blame for the cyberattacks that the DOE seems to have so much trouble reporting correctly.
“It’s probably not Russia or China,” Lewis snipes. “They’ve already gotten everything.”
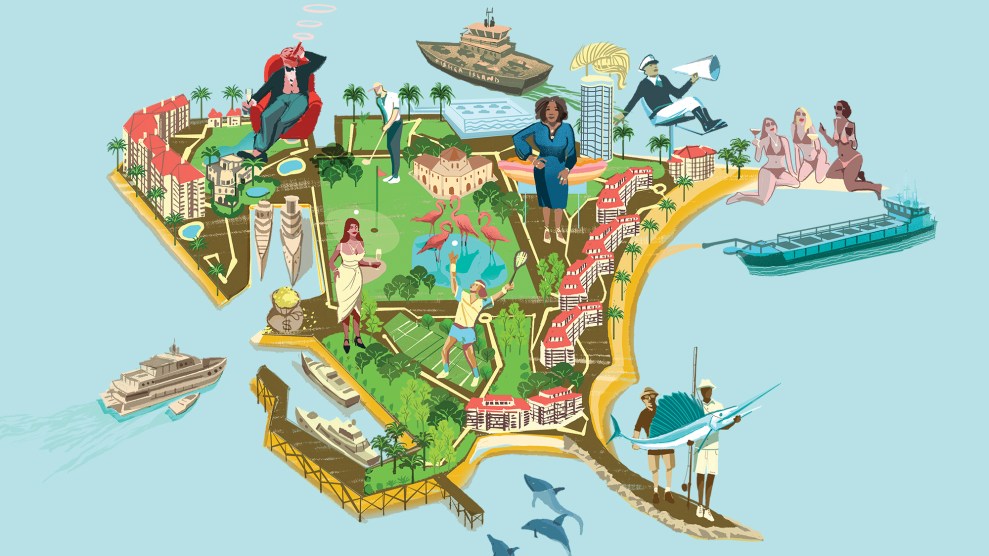
Zoom in on the map below to find the warheads near you as well as the nuclear labs that maintain the stockpile and develop the next generation of atomic weaponry. (For reference, we’ve also included the locations of the nation’s civilian nuclear power plants.)
View Mother Jones: America’s Nuclear Facilities in a full-screen map
Sources: Bulletin of the Atomic Scientists and Federation of American Scientists (PDF), Office of the Deputy Assistant to the Secretary of Defense for Nuclear Matters, Nuclear Energy Institute, United States Nuclear Regulatory Commission, United States Navy.